Archive
Setting a Ldap + Samba PDC –
Throughout all my posts, I wrote too much about Ldap Authentication, therefore, Samba won’t stay out of this party.
Remember, this party is by invitation only :)
You could check out my post about Ldap whether you feel confortable or not, whatever, just follow this post and at the end
you’ll be able to set up a Samba as PDC authenticated by Ldap. This example shown here is based on a minimal installation over Centos 5.3.
Firstly, we need to install all required packages by this example, but there are other things to be done like customizing theboot process.
[root@server ~]# for i in acpid auditd anacron autofs atd avahi-daemon apmd bluetooth cups crond kudzu firstboot iptables ip6tables gpm haldaemon hidd pcscd sendmail yum-updatesd ; do chkconfig $i off ; done
[root@server ~]#
Configure /etc/hosts
[root@server ~]# vi /etc/hosts
192.168.1.3 server server.queiroz.com
Turn selinux off.
[root@server ~]# vi /etc/sysconfig/selinux
SELINUX=disabled
Setting up a PDC with SAMBA under selinux and iptables.
Samba is an emulation to NetBios, a kind of maps (names) where Windows through broadcast can talk to each other. Before that
Internet has grown, Microsoft utilized a protocol called NetBEUI to comunicate to others Windows. Throughout this process of
migration, Novel launched Netware 5 with support to TCP/IP while Microsoft was working to improve Windows NT 3.5 to 4. it’s had
support to TCP/IP.
It’s simple as sound. First of all, there are two daemons incorporated. These are smbd and nmbd.
SMBD is a main samba daemon .
NMDB is a Netbios name service daemon.
First of all, let’s give permissions to samba working behind a firewall.
you can get it running system-config-security-tui or increasing the file /etc/sysconfig/iptables. It’s much better doing the
first one choice.
[root@server ~]# system-config-securitylevel-tui
Go ahead customize option and check samba checkbox followed by OK.
How to set up a DNS server master and slave.
DNS stands for Domain Name Services which means to translate computer names to IP Address. On this post, I’ll explain step by step how to set a Primary DNS and a Secondary DNS replicated by the first one. Both of them have an interactively of syncronizing theirs bases. I’m sure how easy it can be, I hope that to be useful for you.
For this example, I used CentOS-5 as base. So, let’s get started!
PRIMARY DNS SERVER SIDE (WEBSERVER01) (192.168.1.6)
1- Install these following packages
[root@webserver01 ~]# yum install bind bind-utils bind-chroot caching-nameserver
2- Configuring bind as cache name server.
Brief summary of the majors options.
listen-on port 53 – This wanna mean that the service will be running at port 53.
directory – it appoints where it will be stored. Remember, when we install bind-chroot, this isolate BIND in a so-called “chroot jail”, which limits access if DNS is compromissed.
allow-query – it allows machines execute queries on this server
Setting up a Squid Proxy Server – playing with ACLs, passwd file and LDAP Authentication
Hello everyone! Today I’ll blog about squid. I wanna play with ACLs, permissions, authentication based on passwd-file and Ldap. It’s gonna have to be thought pretty much before to implement it, but basically I’ll assume that the ideal environment is this one.
Let’s install it. yum is quite a useful tool :)
[root@webserver01 conf.d]# yum install squid
If you take a look at /etc/sysconfig/squid, you’ll see squid starts without dns resolution. It’s just -D as parameter.
SQUID_OPTS=”-D”
How to configure Virtual Hosts with LDAP and file-based authentication over apache2
Hi all folks. Today I’ll blog about Apache + ssl + VirtualHost and on top of all that I’ll describe how to increase the security based on ldap authentication and password file authentication.
It might be done either installing just the packages which are missing like below,
[root@webserver01 ~]# yum install httpd openssl mod_ssl mod_ldap
or you can try this way.
[root@webserver01 ~]# yum groupinstall WebServer
An Overview of some of the following options.
FollowSymIndex, AllowOverride(None, All, AuthConfig), include, indexoptions, order, allow, deny, DOcumentRoot, ServerAdm, ServerName, AddType, KeepAlive (keep number of conecctions, by default is off.)
FollowSymLinks allows the webserver to use symbolic link.
AllowOverride is related to directory security. It allows you to define a .htaccess to a directory. It can be defined as All, None also Authconfig.
Order defines the access order. it can be Allow and Deny.
include is useful to import others archives. if you wanna import ssl.conf file to httpd.conf, it’s just use include ssl.conf. anything else more than that.
indexoptions is an options that allows you to assign and define an order to index. you can include index.php, index.html. From the moment on a request to some directory and this directory contains one of these ones it will be loaded.
ServerName is a server which responses to this webserver. you can recognize an IP or host named-based.
DocumentRoot means Where are stored the files.
KeepAlive Keep a number of conecctions persistent (more than 1 conecction per user) and by default is off.
Review /etc/hosts, it needs looking like this. I’ll describe to set it up through hosts-based instead of a dns service.
192.168.1.3 webserver01 http://www.test1.com http://www.test2.com
It coud have been set up from the beggining using DNS servers, but don’t be angry, I’ll post something looked like it using bind.
Setting up a Ldap directory service – step by step.
I’m gonna blog and demonstrate in facts how to configure and administrate a LDAP directory services.
Actually, Ldap is a directory service which informations can be stored as a database and through these ones you may recognize you base authentication. This turns out that you could authenticate an user for multiples services.
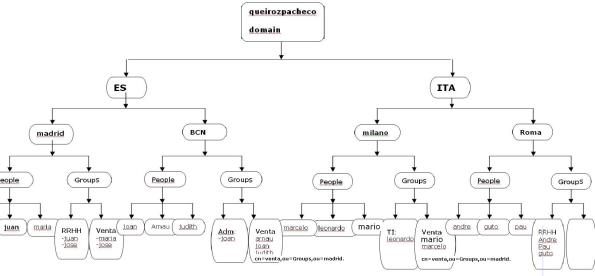
We’re working over the following picture throughout the steps, where it indicates all our ldap tree.
picture1